Настройка Secure Boot
sbctl
sbctl — это удобный менеджер ключей Secure Boot, способный настроить безопасную загрузку,
предлагает возможности управления ключами и отслеживает файлы, которые необходимо подписать в цепочке загрузки.
Установка sbctl
❯ sudo pacman -S sbctlПредварительная настройка
GRUB Boot Manager
Если вы используете GRUB, выполните следующую команду, чтобы включить поддержку Secure Boot в GRUB с использованием ключей ЦС.
❯ sudo grub-install --target=x86_64-efi --efi-directory=/boot/efi --bootloader-id=cachyos --modules="tpm" --disable-shim-lockВход в режим настройки в UEFI
Во-первых, нам нужно перейти в настройки прошивки и установить режим Secure Boot в “Setup Mode”. Вы можете перезагрузиться из уже работающей системы в настройки прошивки с помощью следующей команды.
❯ systemctl reboot --firmware-setup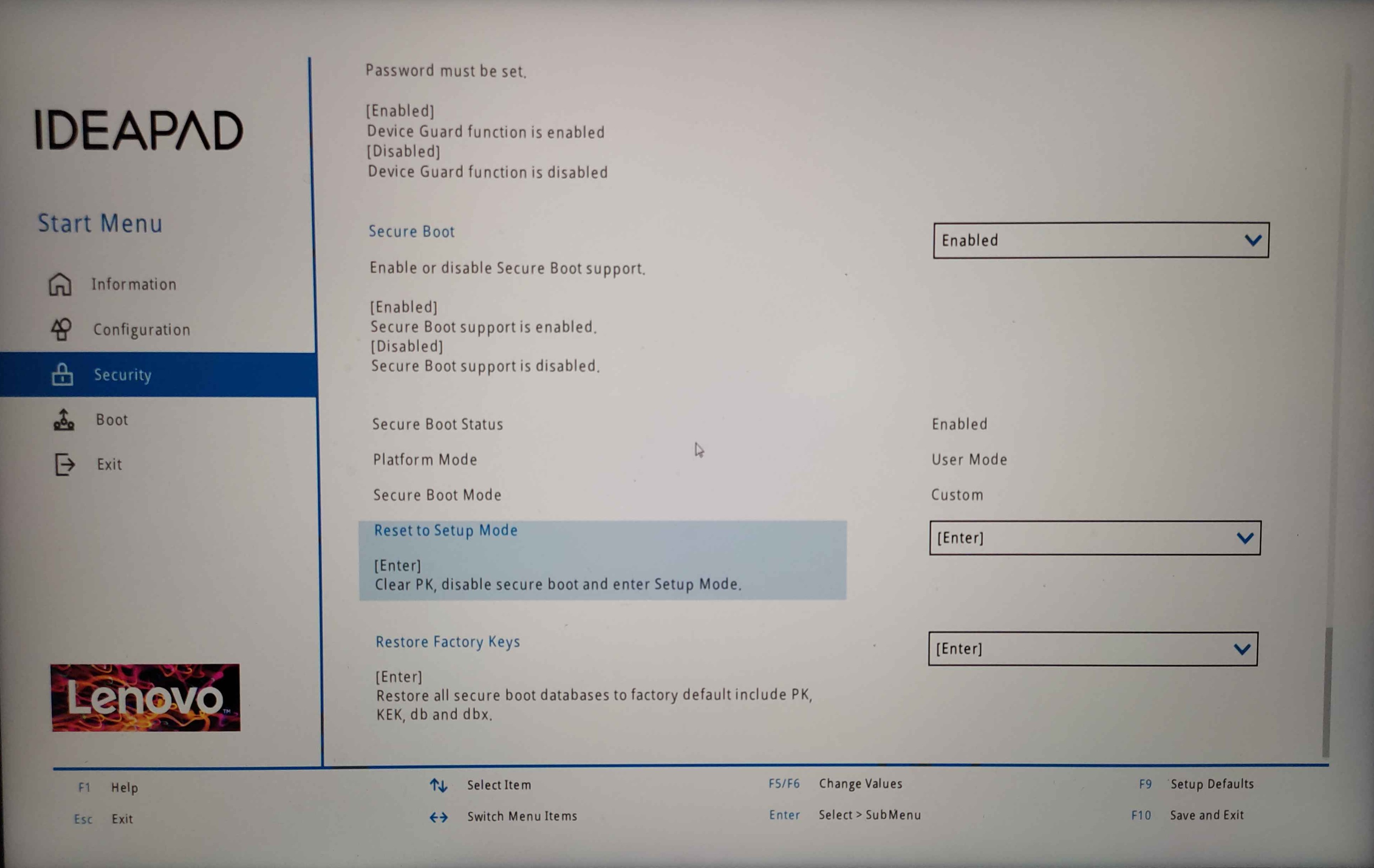
Вот как выглядит BIOS на Lenovo Ideapad 5 Pro. Сбросьте настройки в режим настройки или восстановите заводские ключи и перезагрузитесь обратно в систему.
Настройка sbctl
❯ sudo sbctl status # Если режим настройки включен, мы можем перейти к следующему шагуInstalled: ✘ sbctl is not installedSetup Mode: ✘ EnabledSecure Boot ✘ Disabled
❯ sudo sbctl create-keys # Создайте свои собственные ключи Secure BootCreated Owner UUID a9fbbdb7-a05f-48d5-b63a-08c5df45ee70Creating secure boot keys...✔Secure boot keys created!
❯ sudo sbctl enroll-keys -m # Зарегистрируйте свои ключи с помощью ключей MicrosoftEnrolling keys to EFI variables...✔Enrolled keys to the EFI variables!
❯ sudo sbctl status# Теперь sbctl должен быть установлен, и мы можем перейти к подписанию образов ядра и загрузчикаInstalled: ✔ sbctl is installedOwner GUID: a9fbbdb7-a05f-48d5-b63a-08c5df45ee70Setup Mode: ✔ DisabledSecure Boot ✘ DisabledVendor Keys: microsoftПодписание образа ядра и загрузчика
CachyOS предоставляет скрипт sbctl-batch-sign,
который берет список файлов, которые необходимо подписать, из sudo sbctl verify и подписывает их все.
❯ sudo sbctl verifyVerifying file database and EFI images in /boot...✘ /boot/1c4b5246eef05ac3bc87339323cd5101/6.10.0-cn4.0.fc40.x86_64/linux is not signed✘ /boot/EFI/BOOT/BOOTX64.EFI is not signed✘ /boot/EFI/systemd/systemd-bootx64.efi is not signed✘ /boot/1c4b5246eef05ac3bc87339323cd5101/0-rescue/linux is not signed✘ /boot/1c4b5246eef05ac3bc87339323cd5101/6.10.0-cn3.0.fc40.x86_64/linux is not signed
❯ sudo sbctl-batch-sign
❯ sudo sbctl verifyVerifying file database and EFI images in /boot...✔ /boot/1c4b5246eef05ac3bc87339323cd5101/6.10.0-cn4.0.fc40.x86_64/linux is signed✔ /boot/EFI/BOOT/BOOTX64.EFI is signed✔ /boot/EFI/systemd/systemd-bootx64.efi is signed✔ /boot/1c4b5246eef05ac3bc87339323cd5101/0-rescue/linux is signed✔ /boot/1c4b5246eef05ac3bc87339323cd5101/6.10.0-cn3.0.fc40.x86_64/linux is signedТеперь, когда все файлы подписаны, мы можем перезагрузиться обратно в настройки UEFI и включить безопасную загрузку.
Обратите внимание, что это одноразовый процесс, поскольку подписание файлов с флагом -s сохранит эти файлы в базе данных sbctl.
sbctl поставляется с хуком pacman, что означает, что он будет автоматически
подписывать все новые файлы при обновлении ядра или загрузчика.
systemd-boot
CachyOS использует systemd-boot-update.service, предоставляемый systemd, для обновления загрузчика при перезагрузке. Это означает, что
хук pacman sbctl не будет подписывать обновленные EFI-двоичные файлы. В качестве обходного пути мы можем подписать загрузчик напрямую.
❯ sudo sbctl sign -s -o /usr/lib/systemd/boot/efi/systemd-bootx64.efi.signed /usr/lib/systemd/boot/efi/systemd-bootx64.efiУбедитесь, что безопасная загрузка включена
Чтобы убедиться, что безопасная загрузка действительно включена. Вы можете выполнить одну из следующих команд.
❯ sudo sbctl statusInstalled: ✓ sbctl is installedOwner GUID: a9fbbdb7-a05f-48d5-b63a-08c5df45ee70Setup Mode: ✓ DisabledSecure Boot: ✓ EnabledVendor Keys: microsoft
❯ bootctlSystem: Firmware: UEFI 2.80 (INSYDE Corp. 28724.16435) Firmware Arch: x64 Secure Boot: enabled (user) TPM2 Support: yes Measured UKI: no Boot into FW: supportedСсылки и благодарности
- Arch Wiki заложил основу для этого руководства. Большая часть материала взята оттуда.
- sbctl — это простое руководство по включению поддержки Secure Boot было бы невозможно, если бы не удивительная работа, проделанная для создания этого программного обеспечения.
- Улучшение опыта Secure Boot от Morten linderud — сообщение в блоге Morten
“Foxboron” Linderud о том, насколько сложным был опыт Secure Boot до
sbctl.